1. Create a PuTTY Profile to Save Your Server's Settings
Step 1:
Step 2:
Step 3:
Copy public key to remote server, private key locate in client.
Server side: re-name public key -> authorized_keys, use mv command
# vim /home/huupv/.ssh/authorized_keysFor example authorized_keys file:
ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAQEArPk6AUwiyKwi7zypuERG1+Bjw4dC+aFXJs13hfYsZ//Y30tRJPaivWw8X4444X/nXr1WS3hswFOSrtSXmwOpbN9SvscdqRbKSB9wL/HP1EGRZIonDfZPug48dJ3IUhx4XTtzBeS7q3HODbphTJeWwxwDG40N4hmK8QlMBzxJ5Veue+uxjsDaZsSVLZa2USlP2ggRGXJpJ8nYRGQnGJpBeYtGYn/+EAJ07AgFlQS+M/jkGqaOS1XYWagw== rsa-key-20150224
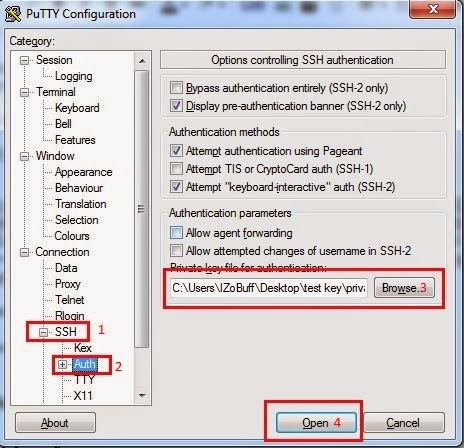
Client side: Hold private key extensive .ppk
Step 4: Connect to remote server
2. Configure sshd_config
# vim /etc/ssh/sshd_configFor example sshd_config file
# Package generated configuration file
# See the sshd_config(5) manpage for details
# What ports, IPs and protocols we listen for
Port 22
# Use these options to restrict which interfaces/protocols sshd will bind to
#ListenAddress ::
#ListenAddress 0.0.0.0
Protocol 2
# HostKeys for protocol version 2
HostKey /etc/ssh/ssh_host_rsa_key
HostKey /etc/ssh/ssh_host_dsa_key
HostKey /etc/ssh/ssh_host_ecdsa_key
HostKey /etc/ssh/ssh_host_ed25519_key
#Privilege Separation is turned on for security
UsePrivilegeSeparation yes
# Lifetime and size of ephemeral version 1 server key
KeyRegenerationInterval 3600
ServerKeyBits 1024
# Logging
SyslogFacility AUTH
LogLevel DEBUG3
# Authentication:
LoginGraceTime 120
PermitRootLogin no
StrictModes yes
RSAAuthentication yes
PubkeyAuthentication yes
AuthorizedKeysFile %h/.ssh/authorized_keys
# Don't read the user's ~/.rhosts and ~/.shosts files
IgnoreRhosts yes
# For this to work you will also need host keys in /etc/ssh_known_hosts
RhostsRSAAuthentication no
# similar for protocol version 2
HostbasedAuthentication no
# Uncomment if you don't trust ~/.ssh/known_hosts for RhostsRSAAuthentication
#IgnoreUserKnownHosts yes
# To enable empty passwords, change to yes (NOT RECOMMENDED)
PermitEmptyPasswords no
# Change to yes to enable challenge-response passwords (beware issues with
# some PAM modules and threads)
ChallengeResponseAuthentication no
# Change to no to disable tunnelled clear text passwords
PasswordAuthentication no
X11Forwarding yes
X11DisplayOffset 10
PrintMotd no
PrintLastLog yes
TCPKeepAlive yes
#UseLogin no
#MaxStartups 10:30:60
#Banner /etc/issue.net
# Allow client to pass locale environment variables
AcceptEnv LANG LC_*
Subsystem sftp /usr/lib/openssh/sftp-server
# Set this to 'yes' to enable PAM authentication, account processing,
# and session processing. If this is enabled, PAM authentication will
# be allowed through the ChallengeResponseAuthentication and
# PasswordAuthentication. Depending on your PAM configuration,
# PAM authentication via ChallengeResponseAuthentication may bypass
# the setting of "PermitRootLogin without-password".
# If you just want the PAM account and session checks to run without
# PAM authentication, then enable this but set PasswordAuthentication
# and ChallengeResponseAuthentication to 'no'.
UsePAM yes
Troubleshooting
Server refused our key
SSH Authentication Refused: Bad Ownership or Modes for Directory
Feb 22 10:15:44 www sshd[2318]: debug3: mm_answer_authserv: service=ssh-connection, style=, role=
Feb 22 10:15:44 www sshd[2318]: debug2: monitor_read: 4 used once, disabling now
Feb 22 10:15:44 www sshd[2318]: debug3: mm_request_receive entering
Feb 22 10:15:44 www sshd[2318]: debug3: monitor_read: checking request 22
Feb 22 10:15:44 www sshd[2318]: debug3: mm_answer_keyallowed entering
Feb 22 10:15:44 www sshd[2318]: debug3: mm_answer_keyallowed: key_from_blob: 0x7f653e401d80
Feb 22 10:15:44 www sshd[2318]: debug1: temporarily_use_uid: 1000/1000 (e=0/0)
Feb 22 10:15:44 www sshd[2318]: debug1: trying public key file /home/huupv/.ssh/authorized_keys
Feb 22 10:15:44 www sshd[2318]: debug1: Could not open authorized keys '/home/huupv/.ssh/authorized_keys': Permission denied
Feb 22 10:15:44 www sshd[2318]: debug1: restore_uid: 0/0
Feb 22 10:15:44 www sshd[2318]: Failed publickey for huupv from 192.168.177.1 port 50057 ssh2: RSA 17:05:6c:1e:fa:d2:e3:fe:02:1f:04:7a:4b:f1:1b:1e
Feb 22 10:15:44 www sshd[2318]: debug3: mm_answer_keyallowed: key 0x7f653e401d80 is not allowed
Feb 22 10:15:44 www sshd[2318]: debug3: mm_request_send entering: type 23
Feb 22 10:15:44 www sshd[2318]: debug2: userauth_pubkey: authenticated 0 pkalg ssh-rsa [preauth]
Feb 22 10:15:44 www sshd[2318]: debug3: userauth_finish: failure partial=0 next methods="publickey,password" [preauth]
Solve problem:
chmod g-w /home/huupv
chmod 700 /home/huupv/.ssh
chmod 600 /home/huupv/.ssh/authorized_keys
Copyright by: www.linuxoperatingsystem.info http://goo.gl/kMscJ4






%2Bubuntu%2B14.10.JPG)


0 comments:
Post a Comment